Introduction to OpenVPN and Other Virtual Private Networks
Virtual Private Networks were first deployed in business settings for remote workers. They have the ability to provide secure access to a local network from a remote computer. Today, VPNs are useful even for common individuals. Masking an IP address, evading geolocation, and using a secure connection are just a few reasons any person may want to use a VPN.
Using a VPN can be as simple as installing a program and clicking a button to connect, but there is a lot more that goes on underneath. There are a few protocols VPNs use. Two different ones are PPTP and IPsec. PPTP or Point-to-Point Tunneling Protocol is an early less secure protocol. PPTP uses a tunnel and encapsulated packets as a means of security. The packets are sent with Point-to-Point Protocol (PPP). These packets are encapsulated by a GRE (Generic Routing Encapsulation) tunnel. Although it is a private connection, it is considered insecure and obsolete because there is no encryption involved.
IPsec stands for Internet Protocol Security. It works at the network layer of the OSI Model. IPsec is thought of as the standard VPN because it can work with any protocol that uses IP. IPsec traffic is secure in that it authenticates the connection and encrypts each packet. IPsec offers two modes, transport mode and tunneling mode. In transport mode, only the payload of the packet is encrypted. This leaves the originating information from the packet visible. The most common mode currently is tunneling mode. This encrypts the entire packet and attaches a new header to the encrypted packet.
I set up my VPN server using an Amazon AWS instance running Ubuntu 14.04 with OpenVPN and easy-rsa. The OpenVPN custom protocol works on layer 2 or 3 of the OSI model. OpenSSL is used to provide authentication and up to 256-bit encryption. It has the capability to authenticate with pre-shared keys, username and password, or certificates. Pre-shared keys are the simplest method when configuring a server and clients.
The initial authentication between a server and client has many checks. The client first initializes a connection to the server. The server then presents its own certificate for the client to authenticate. If the check fails or the certificate is listed as revoked in a CRL used by the client. The client then sends its own certificate to the server for authentication. Each certificate passed by the client or server contains several certificates and keys that are checked. This method is called bidirectional authentication since both sides must present certificates.
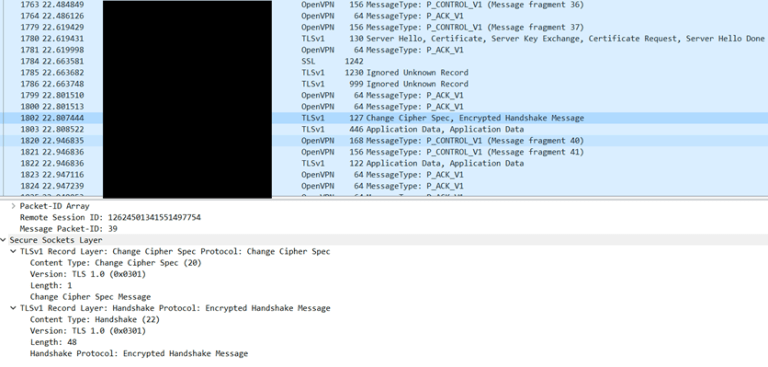
Capture of OpenVPN Connecting
Amazon AWS offers an operating system option specifically for OpenVPN, but I decided to start from stock Ubuntu 14.04 using this tutorial from Digital Ocean. The two packages that need to be installed are OpenVPN and easy-rsa. The first step is to add a rule telling the firewall to forward all traffic from clients. This will ensure that packets do not stop at the VPN server.
After the networking is configured, the Certificate Authority needs to be set up. This is what manages our keys. It’s as simple as entering a city, email, organization, and a few other fields. Running a build-key-server command will generate the certificates and keys for the server side. The build-key with a name argument will generate certificates and keys for one client. This makes it easy to generate different profiles for desktops, laptops, or phones. After generating all of the required files for a client, a single .ovpn profile makes the information easy to store. The tutorial for Ubuntu 16.04 provides a nice script to automate this process. The end format looks like this:
-----BEGIN CERTIFICATE-----
. . .
-----END CERTIFICATE-----
Certificate:
. . .
-----END CERTIFICATE-----
. . .
-----END CERTIFICATE-----
-----BEGIN PRIVATE KEY-----
. . .
-----END PRIVATE KEY-----
OpenVPN client software works on many different devices but I use this VPN on my Windows laptop and Android phone. There is an easy installer for the OpenVPN GUI on Windows. It creates a small icon with a menu in the taskbar. The profile file created earlier goes in the config folder of the OpenVPN folder. The connect option in the GUI shows all profiles in this folder. After connecting, a popup pops up to display the logs as it attempts to authenticate and create a secure tunnel. On Android, the OpenVPN app allows the importing of a .ovpn file. Afterwards, connecting and disconnecting is just a button click away.
Gallery
Encryption and routing do bring downsides to using a VPN. Bandwidth and location often limit speed and increase ping. Sending packets from Rochester to Brazil and back is not a sane thing to do for everyday traffic. In this case, the VPN server is running on a free tier Amazon instance with limited bandwidth as well.
Gallery
Finally, anyone with a tinfoil hat will tell you Amazon keeps their own logs and are not privacy oriented. For recreational use to secure communications, it shouldn’t be a concern. AWS also has the advantage of setting up an instance at any datacenter around the world, for example, Sao Paulo, Brazil. Other hosting providers outside of the United States and a home server are also options.
There are several reasons an everyday person may want to use a secure VPN. When using public Wi-Fi networks, it keeps the connection private and encrypted. It also masks an IP address. Destination addresses only see the IP address of the VPN server, not the client. This can be helpful for mitigating DDOS attacks and hacking attempts. It can also help sidestep geolocation. If content is banned in the current country, connecting to a VPN can act as if the client computer is located in another country. Having an alternate IP address also enables programmers to use one while the other is blocked because of requesting from a website too much for example.
Setting up a VPN is fairly simple at first and has many advanced configurations if curious. It is definitely a quick but worthwhile project that teaches about routing, cryptography, and protocol use.
##Learn More
